Mitigate the Java JMX Agent Insecure Configuration vulnerability in Nessus
Applies to PeerGFS v4.6.0 and earlier. PeerGFS v4.7.0 and later are not affected by this vulnerability.
When using Nessus Scanner to search for vulnerabilities on a server hosting Peer Management Center, it may detect a "Java JMX Agent Insecure Configuration" vulnerability. Details on the vulnerability may look like this:
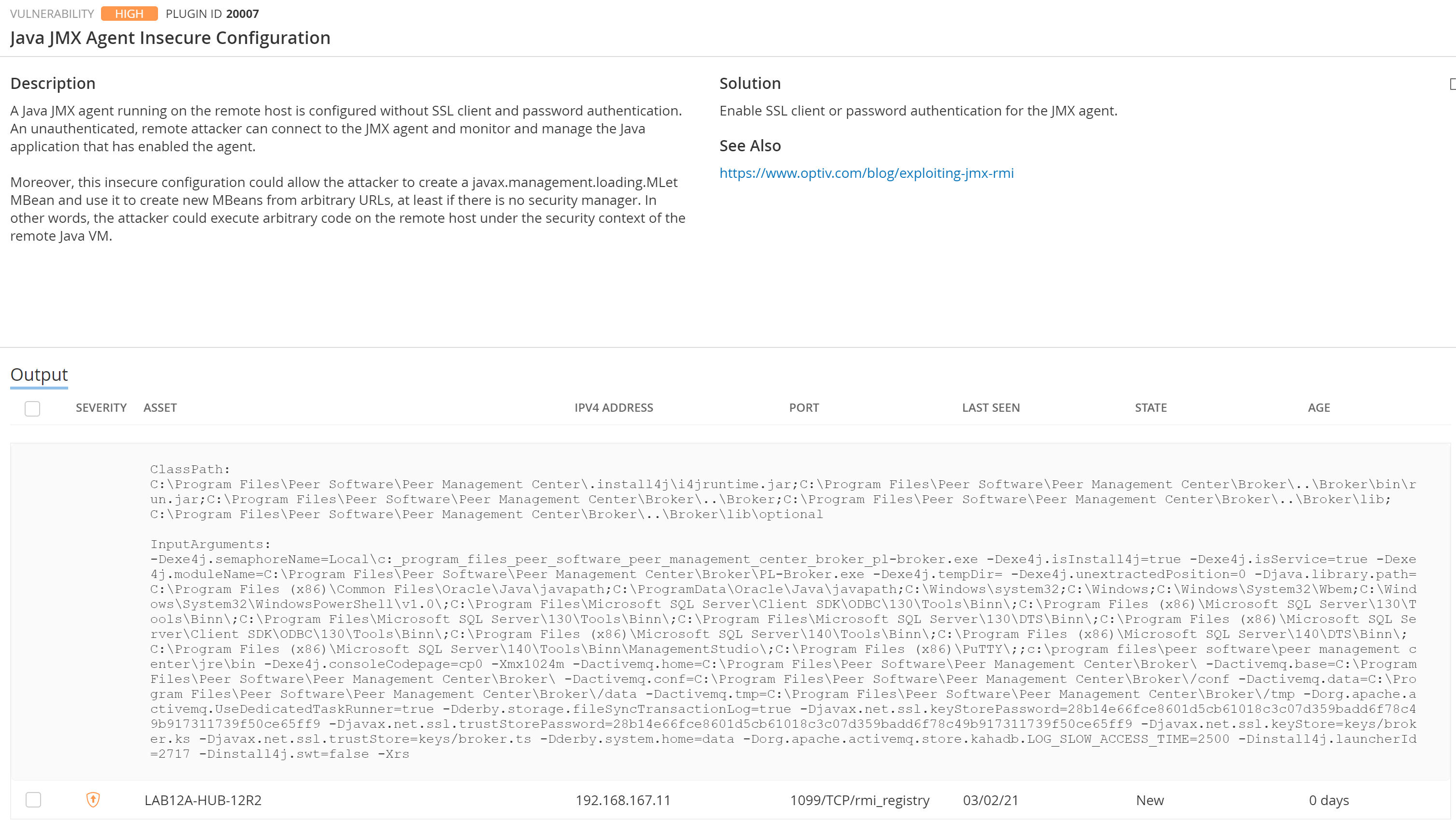
This alert is related to the Peer Management Broker Service and is configured to affect only the loopback address (127.0.0.1) on the server where the PMC is installed. Unfortunately, an issue in ActiveMQ (the broker technology used by PeerGFS) prevents this JMX Agent connection from binding to specific interfaces.
Step-by-step guide
There are two options to mitigate this vulnerability. One involves setting up a firewall rule to fully block remote access to port 1099, while the other involves disabling a diagnostic tool for the Peer Management Broker. The firewall rule is our recommended method.
Option 1: Set up a Windows Firewall rule
Create a new rule in Windows Firewall to prevent access to port 1099 from all IP addresses except the loopback (127.0.0.1) address.
Option 2: Disable the diagnostic tool in the Peer Management Broker
- Use Remote Desktop Protocol (RDP) to access the server where the Peer Management Center is installed.
- Stop all running jobs in the PMC client and stop all Peer Management services.
- Navigate to <PMC Installation Directory>\Broker\conf in Windows Explorer.
- Edit the activemq.xml file in a text editor.
Look for the following line in the xml file:
CODE<managementContext createConnector="true" connectorHost="127.0.0.1"/>Replace this line with the following:
CODE<managementContext createConnector="false" connectorHost="127.0.0.1"/>- Restart the Peer Management services, open the PMC client, and start your jobs.
- Re-run the Nessus scan against the server where the PMC is installed.
Note: Disabling this diagnostic tool will not affect the core functionality of PeerGFS but it will disable the ability to perform some troubleshooting steps with the Peer Management Broker.
